Cleaning up SAN fabric zones and storage array masking views are often a forgotten part of good storage hygiene. Although unused zones and masking views may seem harmless, they pose an availability risk to your environment on multiple fronts.
In my first installment of this series, “Benefits of Storage Capacity Reclamation: Getting Your House in Order Part One,” I used moving from one house to another as an analogy for good storage hygiene. This blog will continue along that path.
While assessing which items to move and which to discard during my home move, I started sifting through my closets. It’s normal to accumulate things over time, but there were numerous items that no longer had any real use. Did I really need to keep this old PS/2 keyboard? Is this old Blackberry charger ever going to be used again? How about the paystubs from 1998?
Similarly, storage configurations can also accumulate a certain amount of detritus over time, even in the best managed environments. I’ve heard this referred to this as “storage creep,” and these accumulated bits and pieces are present in almost every storage environment that I’ve encountered. On the surface, it’s easy to ask what harm they cause and in most cases you would be right. There are two cases, however, where they can present a risk to your environment: Too many zones can cause performance issues and they increase the likelihood of human error when decommissioning or editing zones.
Too Many SAN Fabric Zones Can Cause Issues
Boxes are always a necessity during a house move. We used a lot of boxes that were donated to us by friends, some of which had been used in multiple moves. These veteran boxes sometimes had multiple labels, each from different moves: kitchen, pantry, etc., making it difficult to be sure to which room in the new house they were destined.
My wife asked me to go to the garage where we were staging boxes and take the box labeled “painting supplies” to her office. I went to the garage, saw what appeared to be an appropriately labeled box, and carried the box to her office. When we opened the box we found that instead of painting supplies, it was filled with pet supplies. Further examination showed that “pet supplies” was amongst the multiple labels on the box. I had wasted time and effort bringing her what I thought was the correct box.
A SAN fabric doesn’t necessarily have to have a large number of switches for superfluous zones and aliases to cause problems. Many storage administrators create a new zoning configuration when zones are renamed, added, or deleted, make the current configuration inactive and the new configuration active.
This is sensible, as you have a reversion path if the new configuration causes issues. The problem is that the old inactive configurations may not be removed in a timely manner and leave orphaned zones and zoning configurations on the switch. This makes it easy to make a mistake when manipulating aliases, zones and zonesets.
Do I activate zoneset A_Fab_20210721 or zoneset A_FAB_21JUL2021? Do I add zone z_myserver1_storagearray1 or zone z_storagearray1_myserver1 to the active zoneset?
Ambiguities like these cost time and add risk. If you are in a rush and pick the zoneset you think looks like the correct one, you run the risk of picking the wrong zone and creating a disruption. If you want to be certain and have no risk, you must then look at the configuration of the zoneset, zone, or alias to make sure that you have the correct one, which can be time consuming.
How to Easily Clean Up Superfluous Zones and Aliases
How does one clean these up? One way is to do it manually, which is time consuming, tedious, and has the possibility of errors. Another method is to create your own scripts or other software to automate finding superfluous zones, which is also time consuming. Another option is to go with an off-the-shelf storage performance management solution that has built-in visibility into not only the SAN fabric configuration, but also the storage array configuration.
Figure 1 shows an example of an interactive report generated from IntelliMagic Vision of all zones for which there is no masking view that has both an initiator and target in the zone.

Figure 1: Orphaned Zones
These can be safely deleted, as the zone can in no way create a disruption. And because this analysis is done automatically, the list is always current, and you save precious time writing scripts or looking for these orphaned zones manually
Resolving Configuration Creep in Storage Arrays
Storage array masking views also experience configuration creep for many reasons. Among them are:
- ports may be added or removed,
- server configurations may be improperly configured or decommissioned,
- scripts may misfire and require cleanup,
- etc.
Any of these situations can leave masking views with orphaned ports, which are masking views that don’t have the necessary zoning to support them. Another situation is that masking views without volumes may exist as well.
Like orphaned zones, these can increase the possibility of a mistake being made. Also as with orphaned zones, finding these across multiple storage arrays can be a painstaking and manual task. Figure 2 shows an example of a report showing masking views with orphaned ports and presents it in an easy-to-understand format.
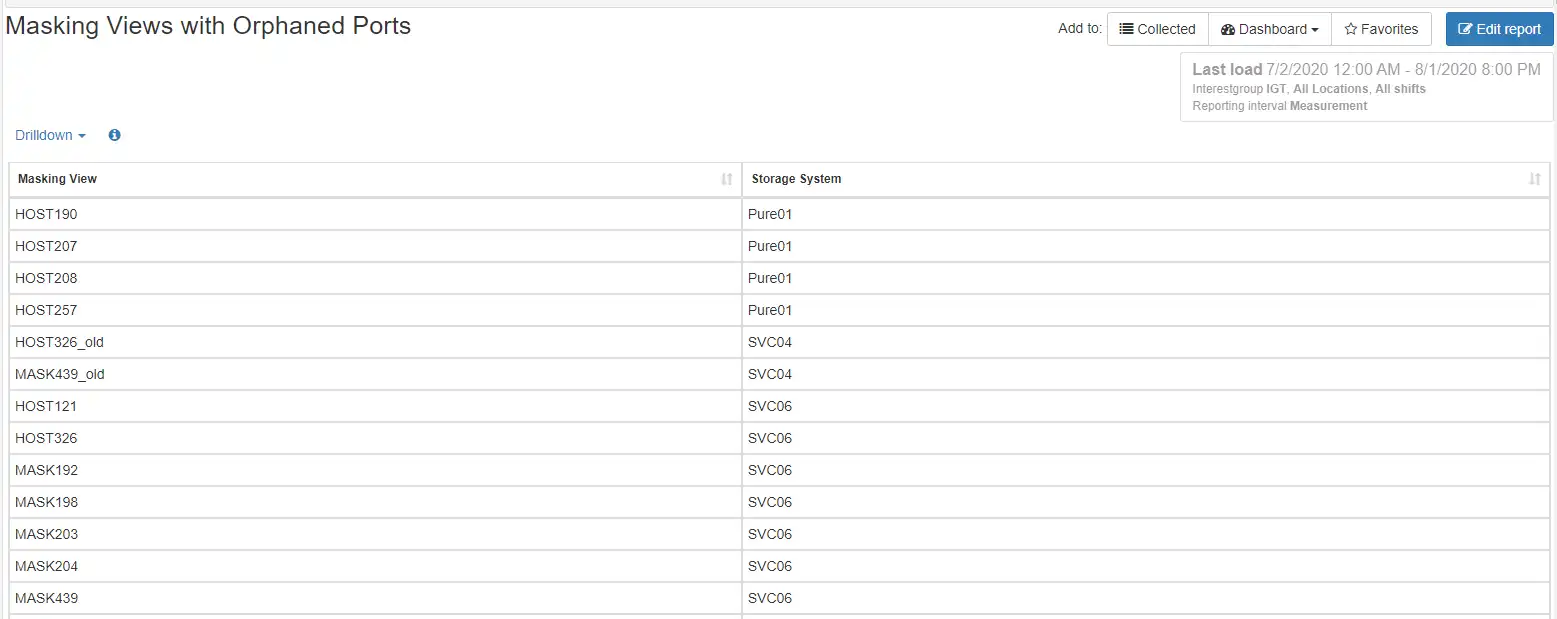
Figure 2: Masking Views with Orphaned Ports
Avoid Hitting the Cisco and Brocade Zoning Database Limits
If I decided to keep one of the superfluous boxes, I had to find a place to put them. At some point, there was not enough space to keep them, and decisions had to be made. This is also the case with zoning configurations.
Both Cisco MDS and Brocade switches have a finite amount of space for the zoning database. Brocade has a 2MB zoning database size with a maximum of 23200 zones. Cisco has a 3.8 MB zoning database size and a maximum of 16000 zones. Once these limits are hit you cannot create new zoning configurations until items are removed from the database. While these limits may seem large, there are cases where it is quite easy to approach or hit the limits:
- These limits are only for the most recent generation of switches. Legacy switches may have smaller databases with lower limits.
- If you have a large SAN fabric with many devices connected and you’re using single target/single initiator zoning.
- If you’re using VSAN (Cisco) or Virtual Fabrics (Brocade).
- If you have numerous inactive configurations on your switches.
Murphy’s law dictates that you will hit these limitations at the worst possible time, which may delay an important corporate initiative or prolong an outage while you remediate. Removing or reducing the amount of unused zoning configurations can help you prevent these types of events.
A Place for Everything and Everything in Its Place
Keeping your SAN fabric and masking views tidy doesn’t have to be a labor-intensive task. IntelliMagic Vision has automatic and up-to-date reports that can help you prevent unexpected downtime and keep your SAN environment clutter free. Learn more about IntelliMagic Vision for SAN here.
This article's author
Share this blog
Related Resources
Improve Collaboration and Reporting with a Single View for Multi-Vendor Storage Performance
Learn how utilizing a single pane of glass for multi-vendor storage reporting and analysis improves not only the effectiveness of your reporting, but also the collaboration amongst team members and departments.
A Single View for Managing Multi-Vendor SAN Infrastructure
Managing a SAN environment with a mix of storage vendors is always challenging because you have to rely on multiple tools to keep storage devices and systems functioning like they should.
Improving Fibre Channel SAN Performance by Reducing Congestion
This whitepaper discusses the causes, troubleshooting, and remediation of congestion on Fibre Channel networks. It will also give some helpful best practices that serve as preventative measures.
Book a Demo or Connect With an Expert
Discuss your technical or sales-related questions with our mainframe experts today

 Tim Chilton
Tim Chilton